Team and Background
why are you the right person / team for this project?
Lay2 is a dev team focusing on blockchain protocols and applications. Our members all have 10+ years R&D experiences in various fields of Internet applications, and have been working in blockchain industry for 2+ years. Lay2’s technology stack in blockchain consists of layer 2 technologies such as lightning network and state channel. We believe that making practical blockchain product is hard but worthy, and have developed a framework and several dapps in payment and games.
Project and Justification
why is this a valuable addition to the Nervos Ecosystem?
Nervos is still at the early stage, and the infrastructure is still incomplete no matter for developer or users. This situation has brought Nervos a bilateral cold start problem: if there are not enough qualified developers to construct the ecosystem, it will be hard to attract users. Simultaneously, without a large number of users, it will be difficult to attract qualified developers. Furthermore, some early public blockchains have established a formidable bilateral ecosystem due to their first-mover advantage and wealth effect. This phenomenon, resulting a network effect, has further exacerbated the difficulty of bilateral cold start of Nervos ecosystem.
Fortunately, the Cell Model and the RISC-V based VM of CKB have brought unprecedented flexibility and extensibility, which makes it possible for Nervos to open a new path. There is no need to wait for facilities such as wallets, DApp browsers, to complete the long process of developing, launching, accumulating applications and attracting users. Instead, Nervos can quickly get access to a large number of users by directly adopting other blockchains’ infrastructure, which means that it could enter the application development stage directly without struggling with the bilateral cold start problem. Lay2 is providing CKB with this capability by originally designed product, pw-sdk.
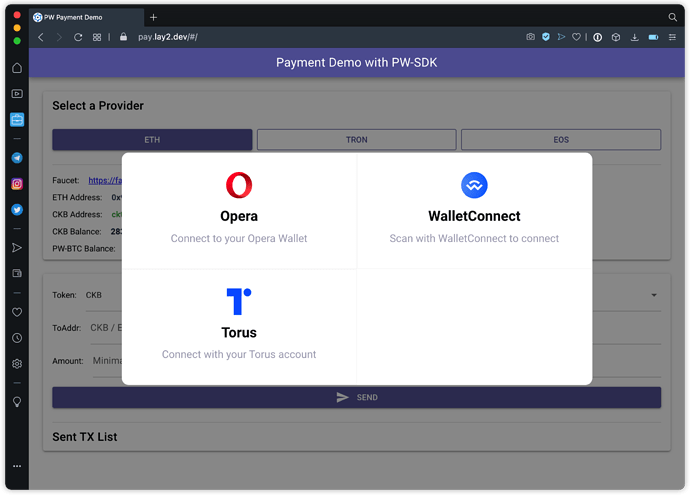
Different from ordinary sdks, DApps developed with pw-sdk (called pw-dapps) can directly run in wallets of Bitcoin, Ethereum, EOS, Tron, etc. There are two meanings of “directly” here: On one hand, no specific development is required of wallet maintainers to support pw-dapps. In fact, they don’t even need to support the CKB chain, e.g. MetaMask can already run pw-dapps now. On the other hand, for blockchain users, any blockchain address is already a valid CKB address, and there is no need to create a CKB wallet before using pw-dapps. Both user experience and security of asset of pw-dapps can be consistent with native DApps on those blockchains.
As for the ecosystem, pw-sdk will bring a large number of mature crypto infrastructures and their user base to Nervos. This allows the construction of Nervos ecosystem to upgrade from a single-threaded serial mode of “infrastructure construction-> product development-> user accumulation-> market feedback" to a multi-threaded mode in which “Infrastructure construction", “product research and development", “market feedback" can advance in parallel. In the same time, it will also largely eliminated the stage of “user accumulation”.It is foreseeable that pw-sdk will greatly accelerate the development of Nervos ecosystem, and It can also show the blockchain world the unique capabilities and great value potential of CKB as a new generation of encrypted economic infrastructure.
Technical Specification and Implementation
how will you implement this successfully?
The pw-sdk includes:
- pw-lib: cryptographic primitives library
Like Keccak-256 hash library which is used to identify the signature of ethereum format, ECDSA Secp256r1(NIST P-256) library, etc.
- pw-lock: universal multi-chain lock script
Pw-lock is able to verify the signatures from wallets of Bitcoin, Ethereum, EOS and other blockchains, and each address (distinguish by public key) of those blockchains can be mapped to a valid CKB address.
Pw-lock will be implemented with type id. We will apply to add pw-lock into the short payload format address standard when it’s stable, therefore the mapped addresses from other blockchains will have the same format as the default CKB address.
- pw-core: front-end sdk
A javascript sdk implemented in Typescript. It will allow developers directly run their CKB DApps in wallets of all blockchains supported by pw-lock, and interact with pw-server.
Timeline / Roadmap
is the timeline reasonable and justified?
It will take about 10 months to get things done, and part of them has been completed so far. As the project progresses, we will continue to release our achievements step by step, so that the community could experience and participate in.
Checkpoint 1: April 2020
pw-lib, including:
- Keccak-256 support
pw-lock, including:
- Ethereum signature support
- EIP-712 support
- Can be deployed with type id
pw-core, including:
- API design
Checkpoint 2: June 2020
pw-lib, including:
- Secp256r1 (ECC P256) support
pw-lock, including:
- Web Authn support
pw-core, including:
- Basic API implementation like signing, sending transactions, etc.
- Basic documents and tutorials
- DApp demo based on pw-core
Checkpoint 3:August 2020
- All pw components will support BTC, EOS and more blockchains.
Checkpoint 4:November 2020
- Full version of pw-lock
- Full version of pw-core
- Documents and demos
Special thanks to @stwith for helping with the translation, to @xxuejie @ash @keith for providing technical support and to all test group members for giving valuable feedbacks.